McAfee’s Mobile Research Team has discovered 280 Android apps that come across as legitimate but are covertly trying to gain access to people’s cryptocurrency wallets.
Cybercriminals have created Android malware which is delivered through harmless-looking apps. McAfee has not published the names of the apps but has revealed that they fall into various categories, including government services, banking and utilities.
The malware primarily aims to obtain the mnemonic phrase, also known as the mnemonic recovery phrase or seed word, for your cryptocurrency wallet. The phrase, which is typically 12, 18, or 24 words, is all that a cybercriminal needs to access your digital assets.
As Beeping Computer notes, since recovery phrases are not necessarily easy to remember, people often take screenshots of their recovery phrases and save them in their galleries.
The malware takes advantage of that by sending all the images stored on a victim’s device to the attackers’ server. Optical character recognition (OCR) techniques are then used to convert the images to text.
How’s the malware spread?
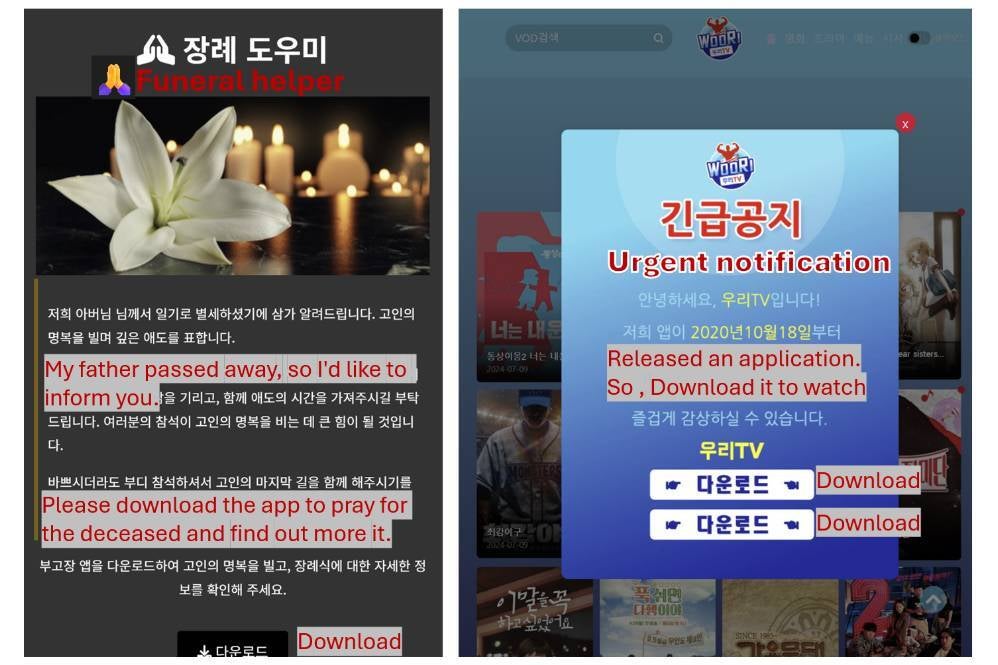
Two fake websites where this Android malware is hosted
The phony apps are not hosted on Google Play. Instead, the links to download are advertised through text messages or social media. Deceptive techniques are often used to trick you into thinking that the link was sent by a reliable source, such as an organization you know or a friend.
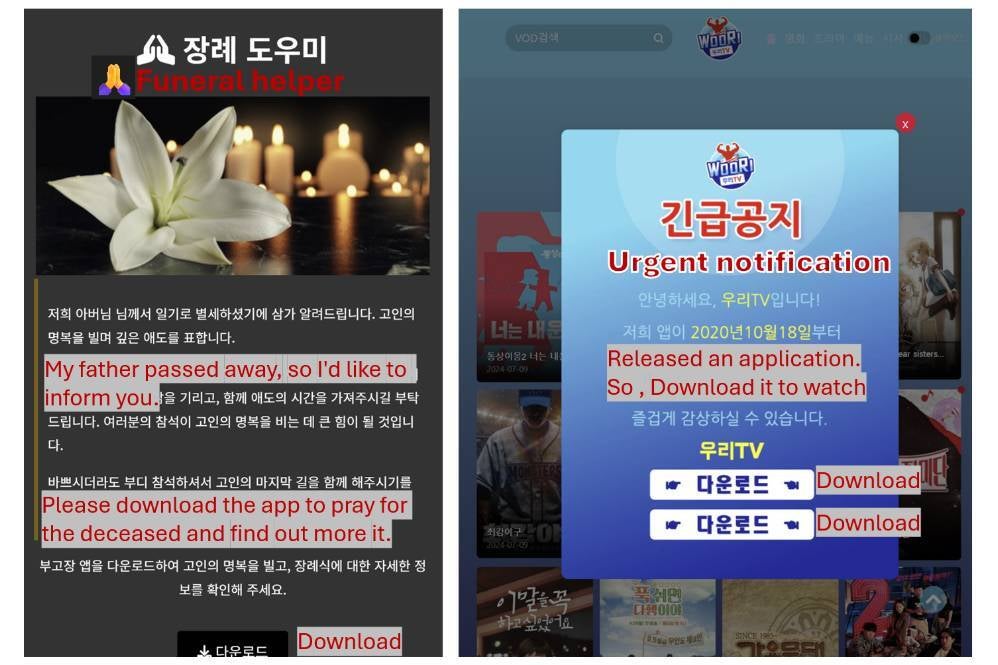
When you click on the link, you are taken to a website that looks authentic. After an app is downloaded, it asks for permission to access sensitive information such as your contacts, text messages, and storage, and to stay active in the background. You are given the impression that the permissions are crucial to the functioning of the app.
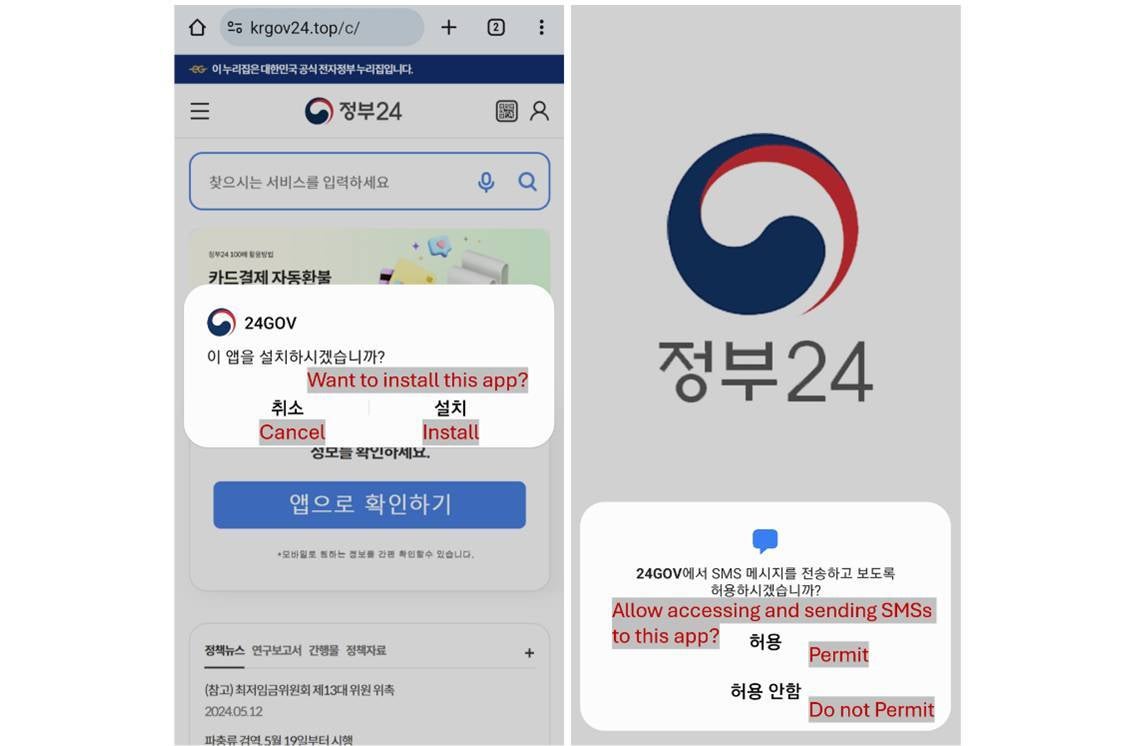
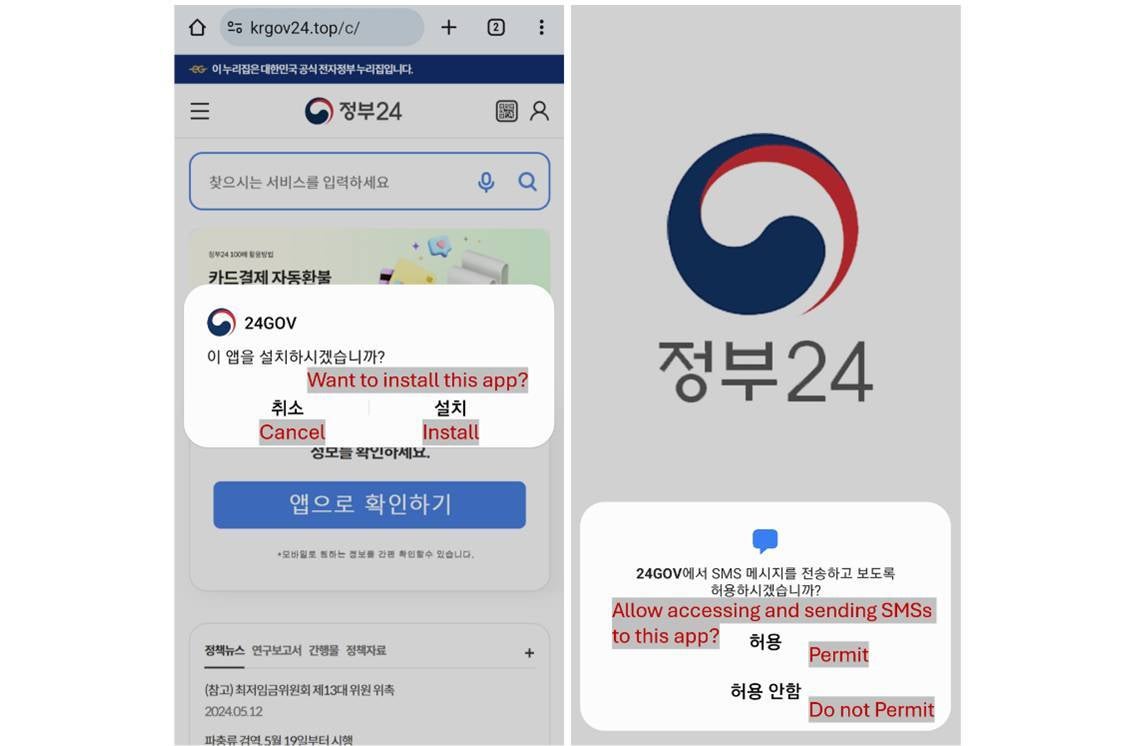
The fake apps trick you into granting sensitive permissions
In addition to covertly stealing your pictures, the apps are also capable of lifting your contacts so that the download link may then be sent to them. The apps also intercept your text messages, giving them the capability to steal two-factor authentication codes.
This malware campaign is primarily targeting users based in Korea but it has recently started to spread to the UK as well. Researchers also found evidence that suggests that the attackers are developing malware for iOS as well.
It’s always best to only downloads Android apps from Google Play. If you recall downloading an app from a third-party source, you might consider deleting it, especially if you have observed odd behaviour such as unexpected redirects or too many loading screens. As an extra step, you should also run a Google Play Protect scan to purge your phone of any malware.